Merkle timber are a elementary a part of what makes blockchains tick. Though it’s positively theoretically doable to make a blockchain with out Merkle timber, just by creating large block headers that immediately include each transaction, doing so poses giant scalability challenges that arguably places the power to trustlessly use blockchains out of the attain of all however essentially the most highly effective computer systems in the long run. Because of Merkle timber, it’s doable to construct Ethereum nodes that run on all computer systems and laptops giant and small, sensible telephones, and even web of issues units equivalent to those who will probably be produced by Slock.it. So how precisely do these Merkle timber work, and what worth do they supply, each now and sooner or later?
First, the fundamentals. A Merkle tree, in essentially the most basic sense, is a means of hashing numerous “chunks” of information collectively which depends on splitting the chunks into buckets, the place every bucket incorporates just a few chunks, then taking the hash of every bucket and repeating the identical course of, persevering with to take action till the whole variety of hashes remaining turns into just one: the foundation hash.
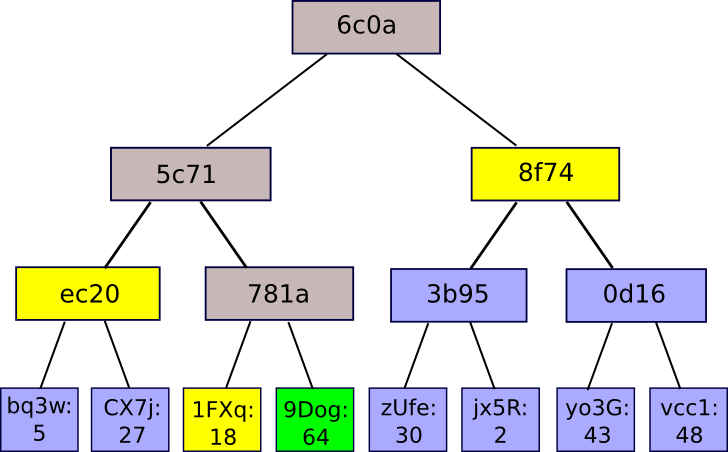
The most typical and easy type of Merkle tree is the binary Mekle tree, the place a bucket at all times consists of two adjoining chunks or hashes; it may be depicted as follows:
So what’s the good thing about this unusual form of hashing algorithm? Why not simply concatenate all of the chunks collectively right into a single large chunk and use an everyday hashing algorithm on that? The reply is that it permits for a neat mechanism generally known as Merkle proofs:
A Merkle proof consists of a piece, the foundation hash of the tree, and the “department” consisting of all the hashes going up alongside the trail from the chunk to the foundation. Somebody studying the proof can confirm that the hashing, no less than for that department, is constant going all the best way up the tree, and subsequently that the given chunk truly is at that place within the tree. The applying is straightforward: suppose that there’s a giant database, and that the complete contents of the database are saved in a Merkle tree the place the foundation of the Merkle tree is publicly recognized and trusted (eg. it was digitally signed by sufficient trusted events, or there may be plenty of proof of labor on it). Then, a person who desires to do a key-value lookup on the database (eg. “inform me the thing in place 85273”) can ask for a Merkle proof, and upon receiving the proof confirm that it’s appropriate, and subsequently that the worth acquired truly is at place 85273 within the database with that specific root. It permits a mechanism for authenticating a small quantity of information, like a hash, to be prolonged to additionally authenticate giant databases of doubtless unbounded measurement.
Merkle Proofs in Bitcoin
The unique software of Merkle proofs was in Bitcoin, as described and created by Satoshi Nakamoto in 2009. The Bitcoin blockchain makes use of Merkle proofs with the intention to retailer the transactions in each block:
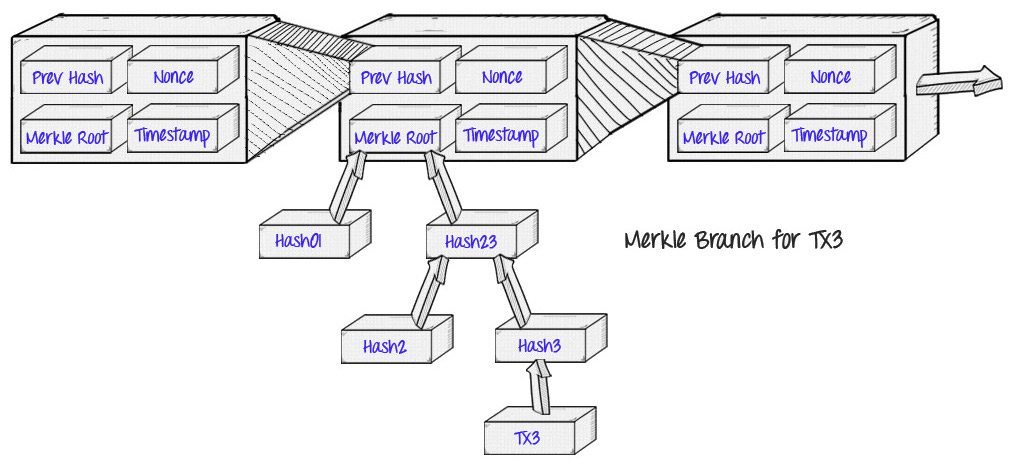
The profit that this gives is the idea that Satoshi described as “simplified cost verification”: as a substitute of downloading each transaction and each block, a “gentle shopper” can solely obtain the chain of block headers, 80-byte chunks of information for every block that include solely 5 issues:
- A hash of the earlier header
- A timestamp
- A mining problem worth
- A proof of labor nonce
- A root hash for the Merkle tree containing the transactions for that block.
If the sunshine shopper desires to find out the standing of a transaction, it may well merely ask for a Merkle proof exhibiting {that a} explicit transaction is in one of many Merkle timber whose root is in a block header for the primary chain.
This will get us fairly far, however Bitcoin-style gentle shoppers do have their limitations. One explicit limitation is that, whereas they will show the inclusion of transactions, they can not show something in regards to the present state (eg. digital asset holdings, title registrations, the standing of economic contracts, and so on). What number of bitcoins do you may have proper now? A Bitcoin gentle shopper can use a protocol involving querying a number of nodes and trusting that no less than one in all them will notify you of any explicit transaction spending out of your addresses, and it will get you fairly far for that use case, however for different extra advanced functions it is not practically sufficient; the exact nature of the impact of a transaction can rely upon the impact of a number of earlier transactions, which themselves rely upon earlier transactions, and so finally you would need to authenticate each single transaction in the complete chain. To get round this, Ethereum takes the Merkle tree idea one step additional.
Merkle Proofs in Ethereum
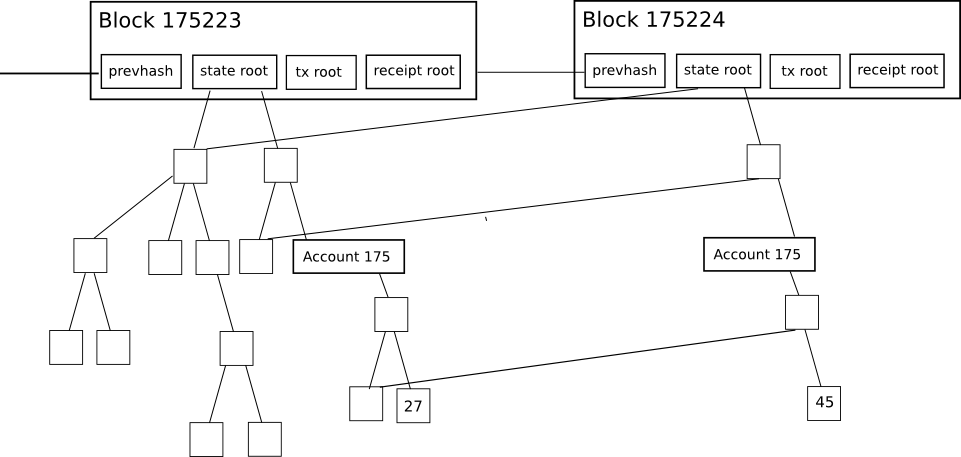
Each block header in Ethereum incorporates not only one Merkle tree, however three timber for 3 sorts of objects:
- Transactions
- Receipts (primarily, items of information exhibiting the impact of every transaction)
- State
This enables for a extremely superior gentle shopper protocol that permits gentle shoppers to simply make and get verifiable solutions to many sorts of queries:
- Has this transaction been included in a selected block?
- Inform me all cases of an occasion of sort X (eg. a crowdfunding contract reaching its objective) emitted by this tackle prior to now 30 days
- What’s the present stability of my account?
- Does this account exist?
- Faux to run this transaction on this contract. What would the output be?
The primary is dealt with by the transaction tree; the third and fourth are dealt with by the state tree, and the second by the receipt tree. The primary 4 are pretty easy to compute; the server merely finds the thing, fetches the Merkle department (the checklist of hashes going up from the thing to the tree root) and replies again to the sunshine shopper with the department.
The fifth can be dealt with by the state tree, however the best way that it’s computed is extra advanced. Right here, we have to assemble what will be known as a Merkle state transition proof. Basically, it’s a proof which make the declare “in case you run transaction T on the state with root S, the outcome will probably be a state with root S’, with log L and output O” (“output” exists as an idea in Ethereum as a result of each transaction is a operate name; it’s not theoretically mandatory).
To compute the proof, the server regionally creates a pretend block, units the state to S, and pretends to be a lightweight shopper whereas making use of the transaction. That’s, if the method of making use of the transaction requires the shopper to find out the stability of an account, the sunshine shopper makes a stability question. If the sunshine shopper must verify a selected merchandise within the storage of a selected contract, the sunshine shopper makes a question for that, and so forth. The server “responds” to all of its personal queries appropriately, however retains observe of all the information that it sends again. The server then sends the shopper the mixed information from all of those requests as a proof. The shopper then undertakes the very same process, however utilizing the supplied proof as its database; if its outcome is similar as what the server claims, then the shopper accepts the proof.
Patricia Bushes
It was talked about above that the best form of Merkle tree is the binary Merkle tree; nevertheless, the timber utilized in Ethereum are extra advanced – that is the “Merkle Patricia tree” that you simply hear about in our documentation. This text will not go into the detailed specification; that’s finest completed by this article and this one, although I’ll focus on the fundamental reasoning.
Binary Merkle timber are excellent information buildings for authenticating data that’s in a “checklist” format; primarily, a collection of chunks one after the opposite. For transaction timber, they’re additionally good as a result of it doesn’t matter how a lot time it takes to edit a tree as soon as it is created, because the tree is created as soon as after which perpetually frozen stable.
For the state tree, nevertheless, the state of affairs is extra advanced. The state in Ethereum primarily consists of a key-value map, the place the keys are addresses and the values are account declarations, itemizing the stability, nonce, code and storage for every account (the place the storage is itself a tree). For instance, the Morden testnet genesis state seems to be as follows:
{
"0000000000000000000000000000000000000001": {
"stability": "1"
},
"0000000000000000000000000000000000000002": {
"stability": "1"
},
"0000000000000000000000000000000000000003": {
"stability": "1"
},
"0000000000000000000000000000000000000004": {
"stability": "1"
},
"102e61f5d8f9bc71d0ad4a084df4e65e05ce0e1c": {
"stability": "1606938044258990275541962092341162602522202993782792835301376"
}
}
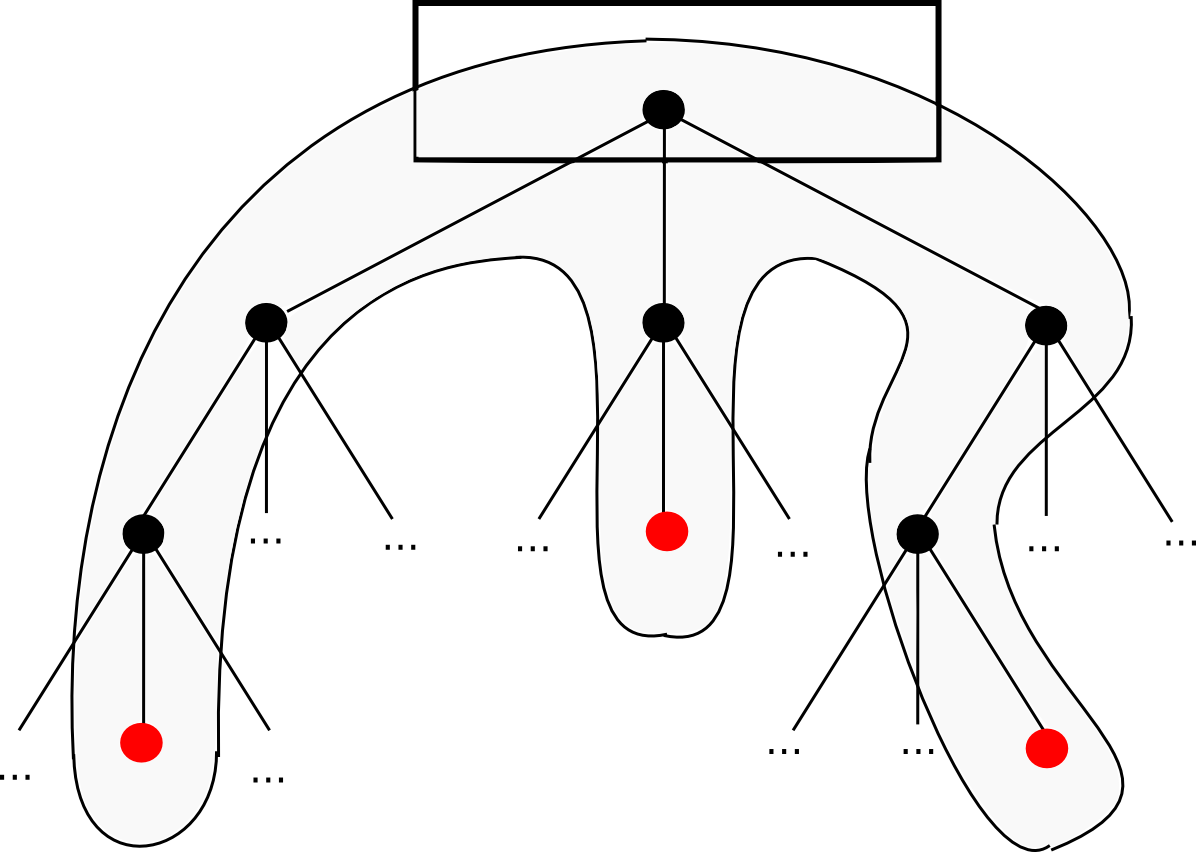
Not like transaction historical past, nevertheless, the state must be ceaselessly up to date: the stability and nonce of accounts is commonly modified, and what’s extra, new accounts are ceaselessly inserted, and keys in storage are ceaselessly inserted and deleted. What’s thus desired is a knowledge construction the place we are able to rapidly calculate the brand new tree root after an insert, replace edit or delete operation, with out recomputing the complete tree. There are additionally two extremely fascinating secondary properties:
- The depth of the tree is bounded, even given an attacker that’s intentionally crafting transactions to make the tree as deep as doable. In any other case, an attacker may carry out a denial of service assault by manipulating the tree to be so deep that every particular person replace turns into extraordinarily gradual.
- The basis of the tree relies upon solely on the information, not on the order during which updates are made. Making updates in a unique order and even recomputing the tree from scratch mustn’t change the foundation.
The Patricia tree, in easy phrases, is probably the closest that we are able to come to attaining all of those properties concurrently. The best clarification for the way it works is that the important thing below which a price is saved is encoded into the “path” that it’s a must to take down the tree. Every node has 16 kids, so the trail is set by hex encoding: for instance, the important thing canine hex encoded is 6 4 6 15 6 7, so you’d begin with the foundation, go down the sixth little one, then the fourth, and so forth till you attain the top. In follow, there are a couple of further optimizations that we are able to make to make the method far more environment friendly when the tree is sparse, however that’s the fundamental precept. The 2 articles talked about above describe all the options in far more element.
